Threat modelling connected and autonomous vehicle cybersecurity: an overview of available tools – Secure-CAV
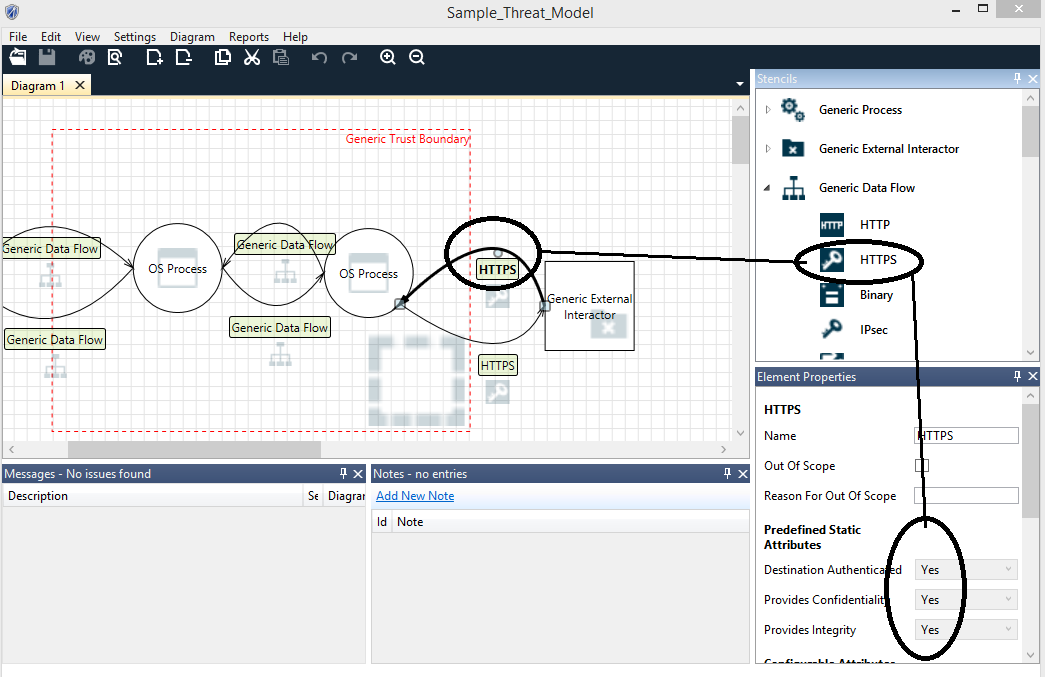
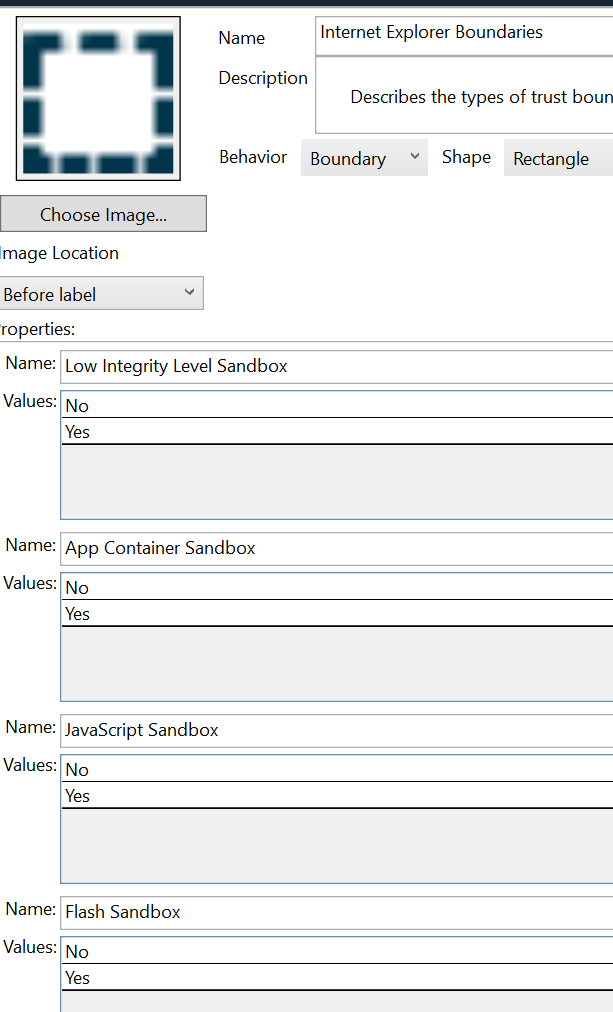
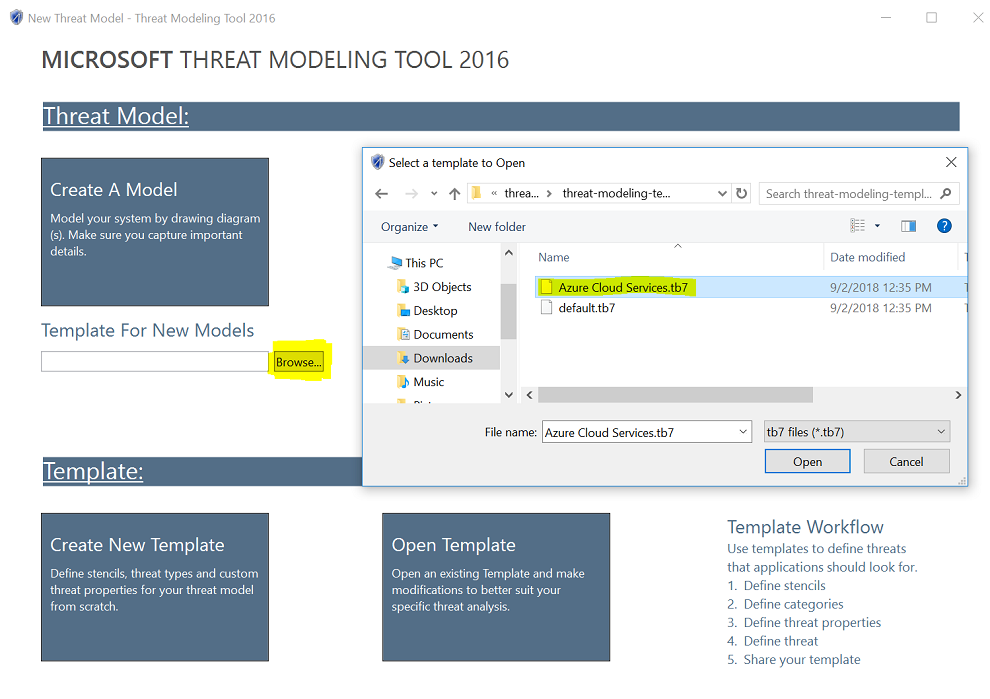
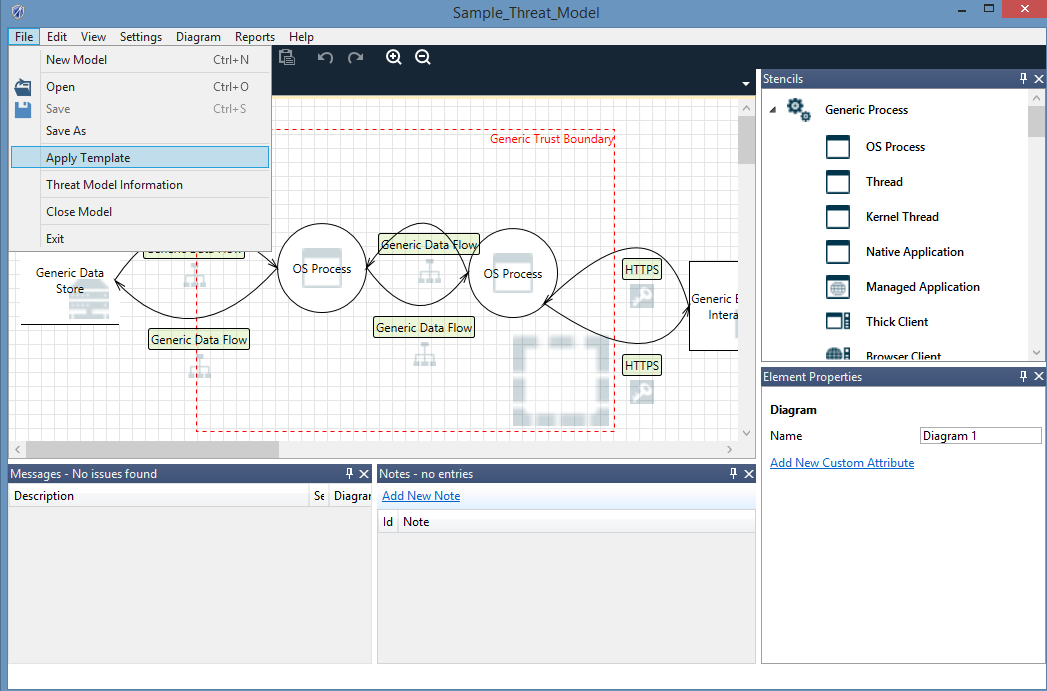
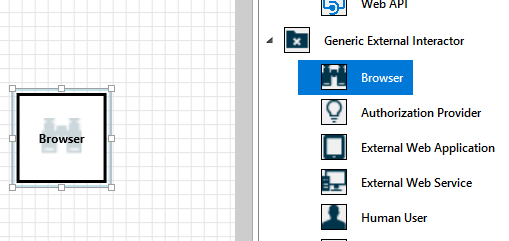
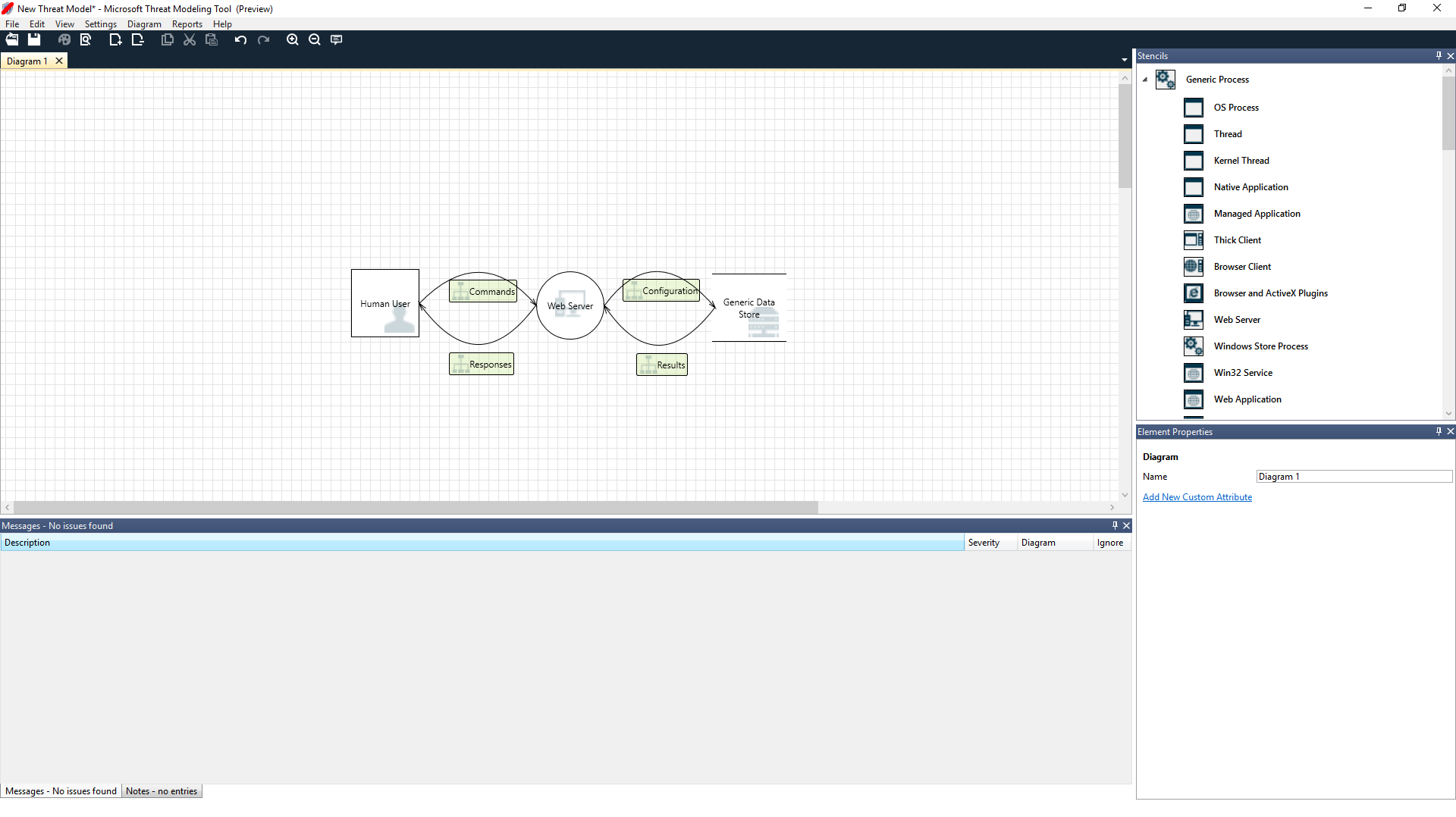
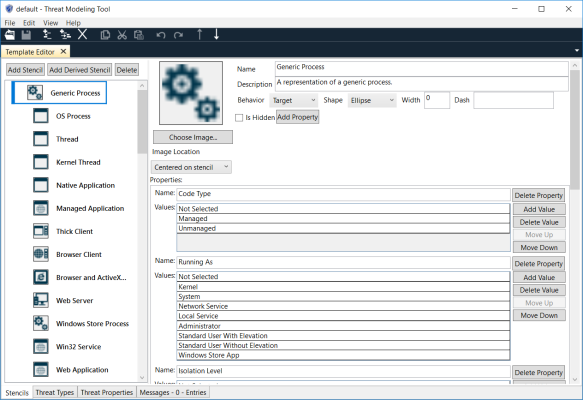
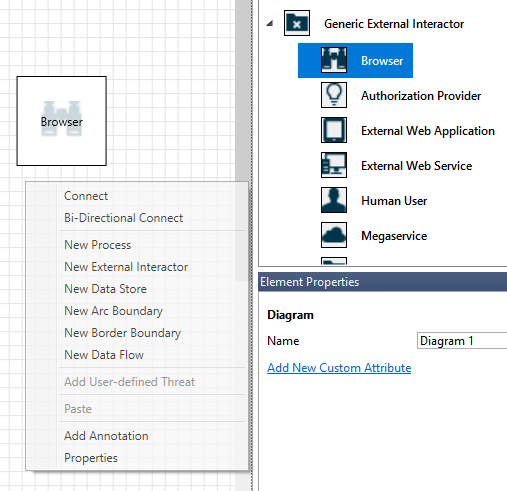
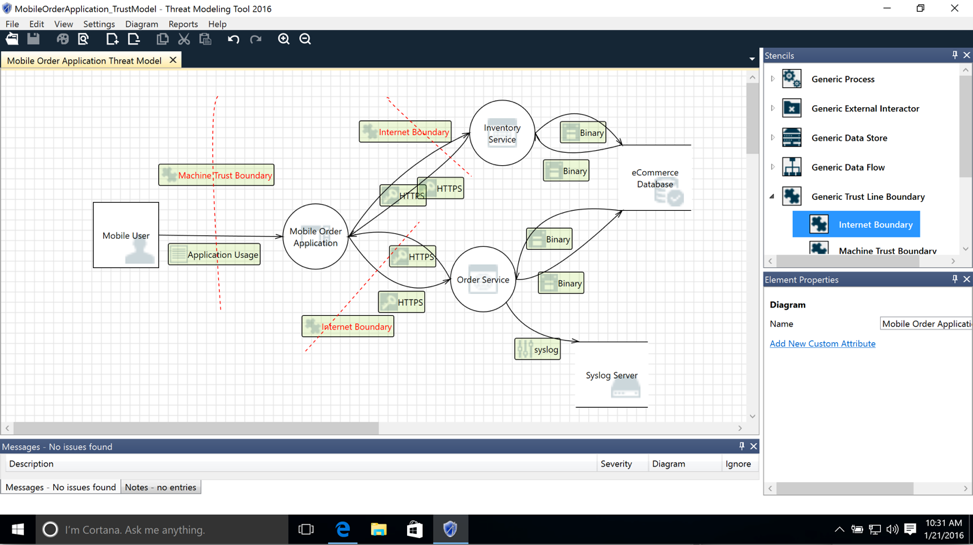
Download Microsoft Threat modeling . Then write to explain why do we need the Microsoft Threat modeling,

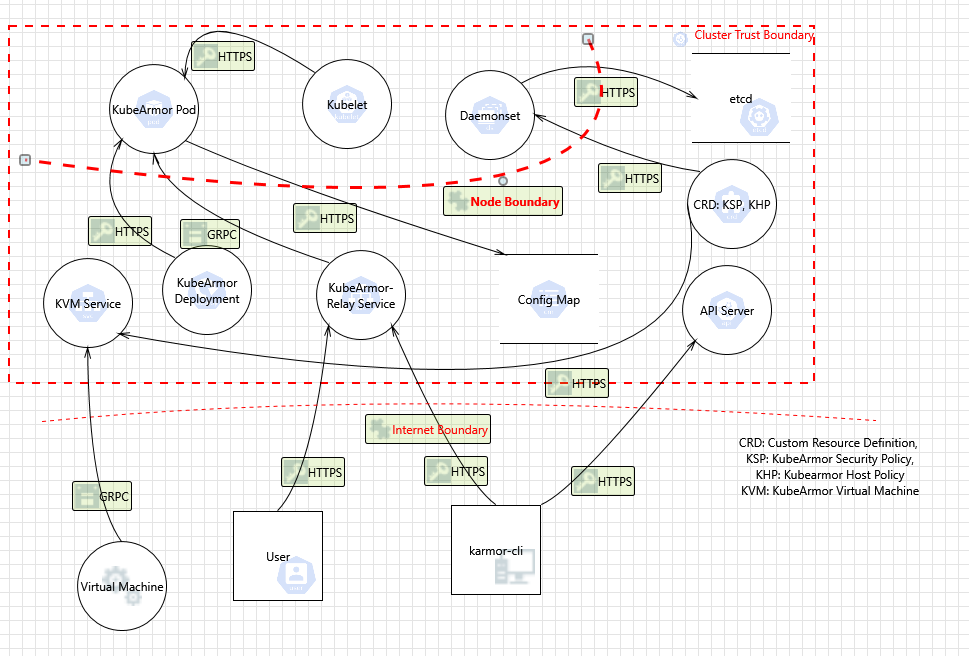
The Automotive Threat Modeling Template | NCC Group Research Blog | Making the world safer and more secure

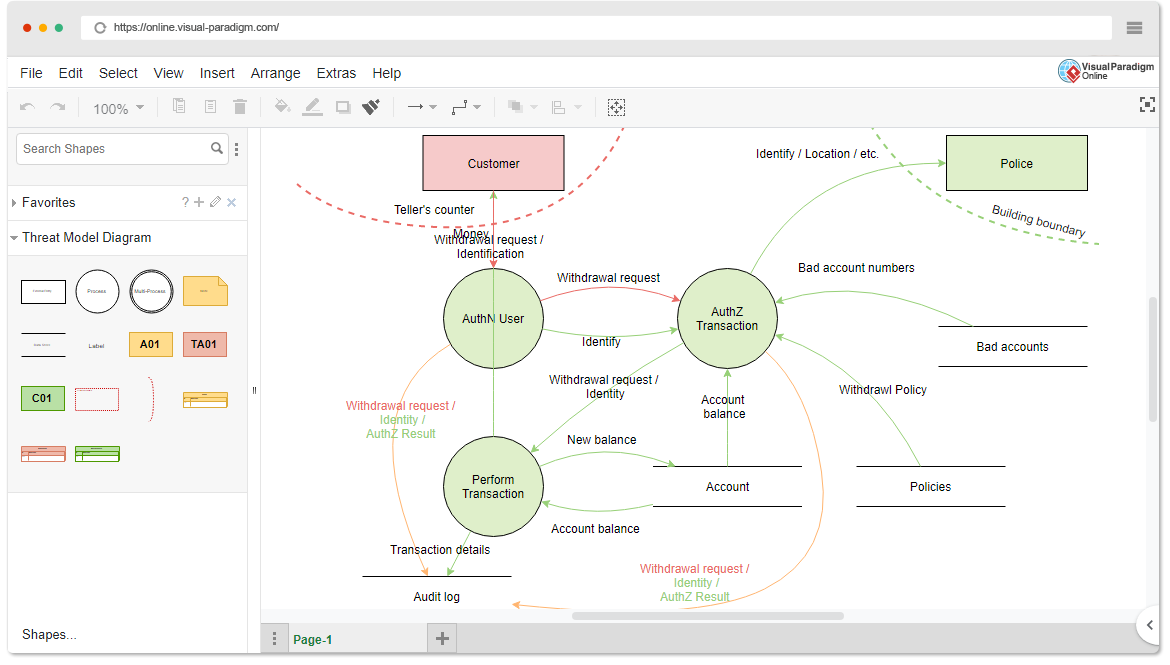
Systematic analysis of automated threat modelling techniques: Comparison of open-source tools | Software Quality Journal
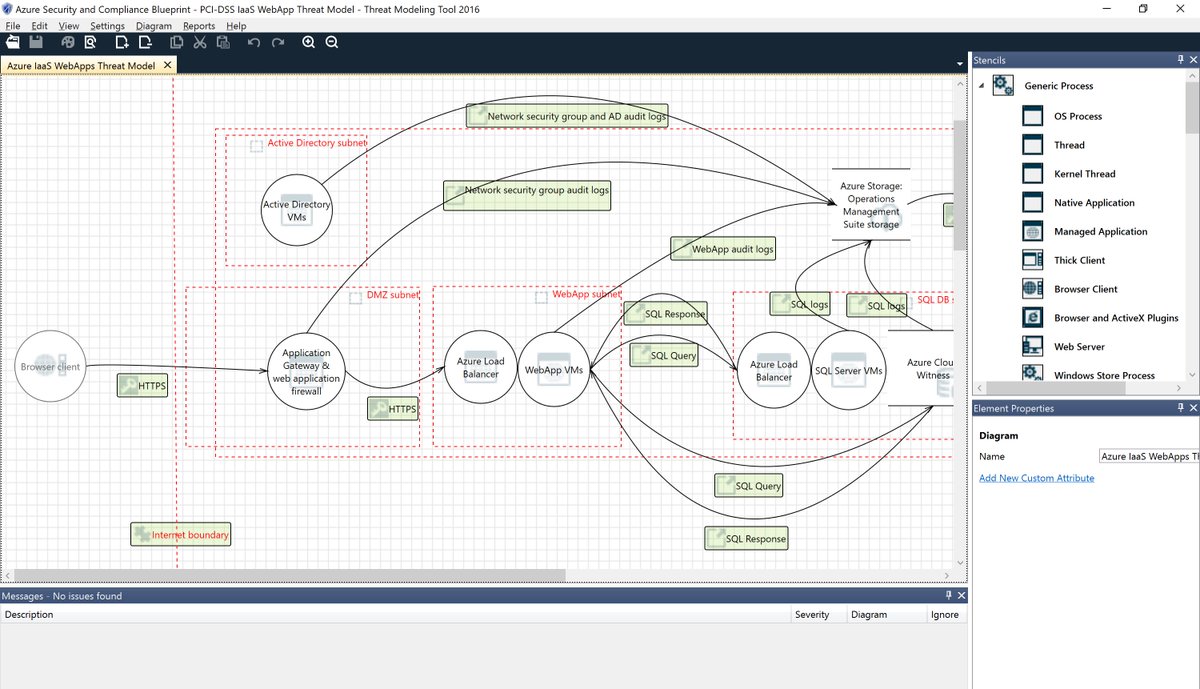
Lennart Passig on X: "Use the #Microsoft #Threat #Modeling #Tool 2016 that helps you finding threats in the design phase of software projects! Very good product after the first initial glance at
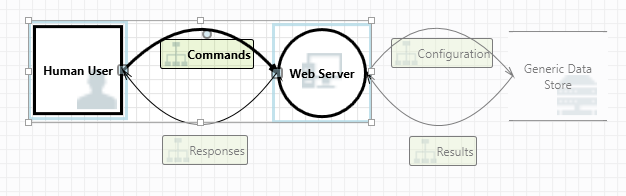

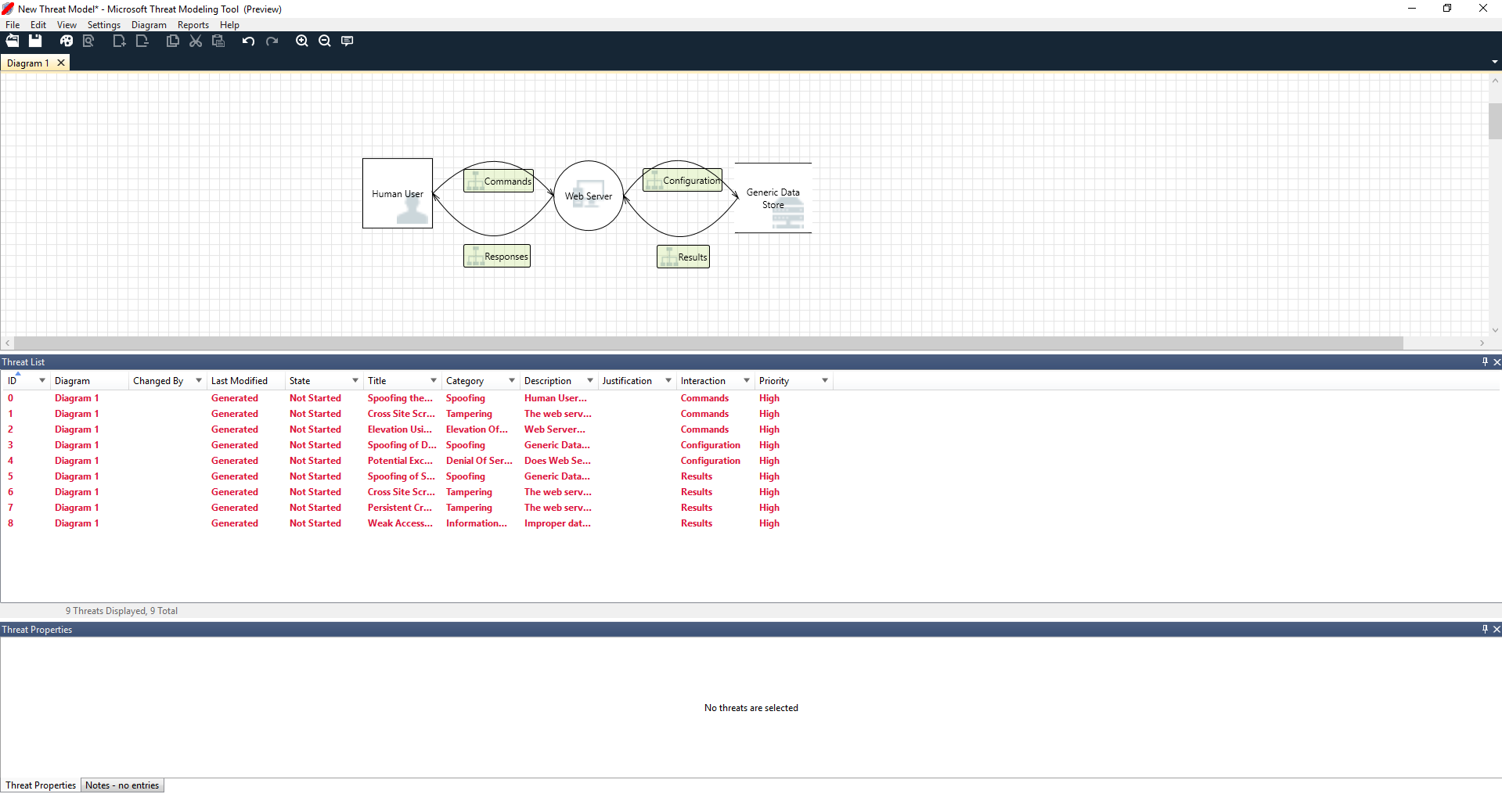






![4. Automated Threat Modeling - Threat Modeling [Book] 4. Automated Threat Modeling - Threat Modeling [Book]](https://www.oreilly.com/api/v2/epubs/9781492056546/files/assets/thmo_0408.png)